On the south side of Chicago, where cracked sidewalks wind between aging apartment buildings and the rhythm of daily life beats to the pulse of resilience, two teenagers quietly rewrote their destinies—and ultimately, the rules of digital entrepreneurship. Their names were Darnell Brooks and Sha Turner. In 2019, they were just fifteen and fourteen, respectively, but their ambitions stretched far beyond the city blocks they called home.
Darnell was the quieter of the pair, a boy who found order in chaos and potential in numbers. His fascination with coding and data sets wasn’t just a hobby—it was a lifeline. Every evening, after the final bell of school, he would disappear into the glow of his secondhand laptop, a gift from his mother, a nurse who worked double shifts to keep their two-bedroom apartment afloat. The device, battered but functional, became his portal to worlds undreamt of in his neighborhood. Online tutorials, programming languages, and digital communities offered him a sense of belonging and purpose that the city’s concrete could not.
Sha, by contrast, thrived in the social realm. Charismatic and quick-witted, he possessed an uncanny ability to read people and situations. Design and branding were his tools—he could transform any flyer, logo, or social media profile into something sleek and professional using nothing but free apps and raw creativity. Sha’s home life, chaotic and fractured, left him to his own devices. He spent hours wandering the streets, soaking up their energy while staying clear of the dangers that ensnared many of his peers.
Their friendship was forged years earlier at a community center tech repair workshop. While other kids grew bored and drifted away, Darnell and Sha stayed late, dissecting old computers and experimenting with makeshift circuits. The contrast in their skills made them a natural team: Darnell’s technical precision paired perfectly with Sha’s flair for presentation and strategy. Over time, their bond deepened into a partnership, bound by the shared conviction that they could rise above their circumstances.
Unlike many of their peers, Darnell and Sha weren’t tempted by quick-money schemes. They saw older kids flipping sneakers, fixing phones, or reselling concert tickets, but they wanted something more sustainable—something that wouldn’t risk their future. They spent afternoons brainstorming, scouring the internet for inspiration, searching for their breakthrough.
One day, Sha stumbled upon a viral video showcasing teenagers making money online by selling digital products—ebooks, graphic templates, study guides. The idea electrified them. Sha was eager to put his branding skills to work, and Darnell’s technical know-how made the systems required seem possible. After weeks of planning, they launched a modest online business selling study guides for popular school subjects. Their early efforts were clumsy: the guides were simplistic and the website lacked polish. Yet Sha’s social media marketing skills brought in their first customers, and to their surprise, the guides started selling.

Each sale felt like a victory—a proof that their ideas could work. But the market was crowded, and competition was fierce. Their business needed more than flashy ads and hard work; it needed a unique angle. Darnell, ever analytical, began researching ways to streamline their operations. Automation seemed the obvious solution, and he dove into forums and tutorials, learning to reduce the time and effort required for manual tasks.
It was during one of these late-night sessions that Darnell stumbled upon something unexpected: an underground market for educational platform accounts. The forums he found were filled with discussions about selling access to premium online learning services—platforms that charged hefty monthly fees for resources like ebooks, video tutorials, practice exams, and even one-on-one tutoring. Users sold accounts for a fraction of the cost, often created using stolen data or exploiting free trial loopholes.
At first, Darnell dismissed the idea as too risky and unethical. But curiosity gnawed at him. The sheer size of the market was staggering—thousands of people actively seeking these accounts, and many sellers operating with apparent impunity. The justifications offered fascinated him. Some claimed they were helping students who couldn’t afford expensive subscriptions. While Darnell wasn’t convinced by these arguments, the opportunity was undeniable.
He shared his findings with Sha, knowing his friend’s knack for spotting profitable trends could help refine the idea. Sha’s reaction was immediate—he saw potential not only in the concept but in how they could market it. Unlike the shady, poorly designed websites common in the resale market, Sha envisioned a sleek, professional platform that would appeal to budget-conscious students. As they discussed the risks, Sha argued that they wouldn’t be hacking into accounts or stealing data themselves. Instead, they would automate the creation of free trial accounts—the same accounts the platforms already offered. Sha reasoned that since these accounts were technically free, reselling them wasn’t truly theft.
The more they debated, the more they rationalized their decision. They convinced themselves it was a victimless crime. The companies were massive, the resources were digital, and no one was directly harmed. Once they decided to move forward, Darnell began building the tools they needed. Using his coding skills, he wrote scripts that automated the process of creating free trial accounts for a popular online learning platform, generating dozens in minutes. Sha, meanwhile, focused on branding, designing a polished website that marketed the accounts as affordable educational solutions and emphasized convenience and legitimacy.
Together, they crafted a pricing strategy that undercut subscription costs but still yielded significant profits. Their first few sales were cautious experiments, using anonymous payment platforms like cryptocurrency wallets to process transactions and ensure their identities remained hidden. To their surprise, customers responded immediately—students, parents, and even small tutoring centers began purchasing accounts in bulk. The low price point made their service appealing, and the seamless user experience Sha had designed gave the business a veneer of credibility.
As orders increased, the boys realized they needed to scale up. Darnell improved his scripts to generate thousands of accounts at a time, while Sha expanded their marketing reach, using social media platforms and forums to attract more customers and create buzz around their service. They reinvested profits into tools like VPNs to mask their activities, bulk email services to handle customer inquiries, and even better laptops to keep up with demand.
Within weeks, their small operation transformed into a thriving enterprise. Orders flooded in daily, and money poured into their anonymous accounts faster than they could spend it. They began to see themselves not as criminals, but as entrepreneurs who had cracked the code of a broken system. They believed they were offering a service that met a real demand, justifying their actions as resourceful rather than fraudulent.
As the operation grew, so did its complexity. Darnell and Sha found themselves managing inventory, customer service, and marketing while constantly refining their methods to stay ahead of detection. What had started as a side hustle to supplement their study guide business quickly became their primary focus. They weren’t just running a scam—they were building a brand.
By the end of their first month, the boys had earned more money than either of their families had seen in years. The thrill of success was intoxicating. They reinvested in their operation, confident they had created a system that was virtually foolproof. What they didn’t realize was that their perfect plan was already leaving breadcrumbs for anyone determined enough to follow. For now, however, they were riding high, convinced they had unlocked a shortcut to success.
As months passed, Darnell and Sha’s operation evolved into an unexpectedly successful enterprise. What began as a niche market selling accounts for one educational platform rapidly expanded into a diversified business. Sha’s marketing ingenuity played a crucial role in this growth. Using social media and online forums, he crafted campaigns that made their service appear not only legitimate but indispensable. Their website’s sleek design and professional tone attracted a steady stream of customers, many of whom shared the link with others. Within weeks, traffic to the site skyrocketed, with thousands of visitors browsing their offerings daily.
To meet demand, Darnell and Sha knew they had to streamline operations. Sha, ever the strategist, suggested hiring a virtual assistant. They found someone overseas willing to manage customer inquiries for a fraction of the cost they were earning. The assistant’s role was simple: respond to questions, handle complaints, and maintain a sense of legitimacy for their business. This addition allowed Sha to focus on marketing and expansion while Darnell worked on the technical side.
Darnell used their growing profits to invest in better tools. With his new laptop and a faster internet connection, he refined his scripts to automate account creation across multiple platforms. No longer limited to educational accounts, the boys added access to streaming services, ebook libraries, and even premium software trials to their catalog. Each addition was carefully researched to ensure it would appeal to their growing customer base. They also diversified payment options, integrating cryptocurrency wallets and prepaid cards to increase convenience and reduce traceability.
The money rolled in faster than they had anticipated. At first, they treated their profits cautiously, reinvesting into the business and keeping expenditures modest. However, as their earnings grew, so did their confidence. They began indulging in luxuries they’d once only dreamed of. Sha upgraded his wardrobe, sporting designer sneakers and streetwear that turned heads at school. Darnell, while more reserved, bought cutting-edge gaming equipment and a new phone. Their sudden affluence didn’t go unnoticed by their peers, sparking both admiration and curiosity.
Despite their success, managing the operation became increasingly challenging. The influx of orders meant more logistical hurdles—from ensuring timely delivery of account details to handling customer disputes. Darnell, always meticulous, insisted on keeping detailed records of their transactions. He encrypted everything from customer lists to payment logs using software he taught himself to operate. To him, these records were essential for maintaining control and identifying patterns that could help them improve their operation. Sha, on the other hand, concentrated on customer satisfaction, ensuring that buyers felt confident enough to return. He knew that keeping complaints to a minimum was critical to avoiding unwanted scrutiny.
Darnell grew increasingly paranoid, urging Sha to scale back their advertising to avoid drawing too much attention. Sha, ever optimistic, dismissed these concerns, believing that their professional image would shield them from suspicion. As the complexity of their business grew, so did the pressure. Their days became a blur of balancing schoolwork, maintaining the website, managing customer inquiries, and troubleshooting technical issues. Darnell often worked late into the night, tweaking scripts and monitoring account activity to ensure nothing slipped through the cracks. Sha spent hours crafting marketing campaigns and responding to customers. Both boys felt the weight of their double life, though neither was willing to admit it. The sheer scale of their operation made it increasingly difficult to stay anonymous.
Yet for now, the boys were riding a wave of success, earning more money than they’d ever imagined. They believed they had built an unbreakable system—one that could sustain their growing ambitions. What they didn’t realize was that their rapid rise had also made them visible to the very entities they had worked so hard to avoid.
By late 2021, Darnell and Sha’s operation was running at full capacity, generating a steady stream of income that exceeded anything they had imagined. Their website was thriving, and they had built a reputation among their customers for reliability and affordability. Yet in the background, the very platforms they exploited were beginning to take notice.
The trouble began with the educational platform that had served as the foundation of their business. Its security team had been tracking unusual activity for weeks—an unprecedented surge in trial account signups originating from a single geographic area. These accounts exhibited distinct patterns: identical naming conventions, similar IP address ranges, and unusually rapid creation speeds. Recognizing the signs of automated fraud, the team initiated an internal investigation, using advanced algorithms to trace the source of the accounts. Their analysis led them to a cluster of IP addresses originating from Darnell and Sha’s neighborhood.
Simultaneously, trouble was brewing on another front. A disgruntled customer, frustrated after their purchased account was disabled within hours of activation, filed a formal complaint. This customer, unlike most others, wasn’t content with a refund or apology. Instead, they escalated their concerns to the company’s legal department, providing screenshots of the transaction and links to the boys’ website.
The combination of the internal investigation and this external complaint raised a red flag that couldn’t be ignored. Unaware of the brewing storm, Darnell and Sha continued their work as usual. They viewed the occasional flagged order or refund request as minor hiccups, not realizing these disruptions were symptoms of a larger problem.
However, the signs of trouble became harder to ignore. Accounts were being flagged faster, with some disabled within minutes of being sold. Payment processors occasionally delayed transactions, citing suspicious activity. Sha dismissed these incidents as technical glitches, but Darnell’s natural caution made him uneasy.
Darnell began noticing other patterns that fed his paranoia—emails from the educational platform hinted at potential legal action, warning of violations of their terms of service. While the messages were likely automated, their increasingly frequent arrival put Darnell on edge. He shared his concerns with Sha, but his partner, ever confident, brushed them aside. Sha believed their anonymity and professional presentation would shield them from scrutiny. He argued that the platform’s sheer size and the volume of trial accounts being created worldwide made it impossible to pinpoint their involvement.
Despite Sha’s reassurances, Darnell took precautionary steps. He began deleting older records, wiping transaction logs, and encrypting any sensitive files he couldn’t bring himself to erase completely. His instinct for self-preservation clashed with Sha’s focus on expansion, creating subtle tension between the two. Sha saw Darnell’s precautions as unnecessary, even wasteful, but he didn’t interfere.
Meanwhile, the company’s legal department had begun connecting the dots. The complaint from the disgruntled customer provided a direct link to the boys’ website. Investigators cross-referenced the site with data from their internal security team, confirming that the fraudulent accounts were tied to the same operation. The website’s professional design and low prices suggested that whoever was behind it had both technical expertise and significant resources. The company, now aware of the scope of the fraud, flagged the operation as part of a larger scheme requiring external intervention.
For Darnell and Sha, the first tangible signs of trouble came when payments from their website began experiencing frequent delays. These disruptions, though small at first, quickly escalated. Some payment processors suspended their accounts, citing violations of terms of service. Customers started noticing accounts that didn’t work as promised, slower responses to inquiries, and occasional unexplained outages on the website. These issues, though minor in isolation, began chipping away at the boys’ once untouchable reputation.
As the disruptions mounted, Darnell’s anxiety grew. He began to question the sustainability of their operation and wondered if they had underestimated the risks. Sha, however, maintained his unwavering optimism. He focused on damage control, reassuring customers and adapting their marketing strategies to keep the momentum going. To him, the setbacks were nothing more than obstacles to overcome.
Unbeknownst to both boys, their operation was already under surveillance. The company had escalated the case to cybersecurity specialists, who worked to pinpoint the individuals responsible. Investigators monitored the website’s activity, tracked payment flows, and compiled a growing dossier of evidence. While Darnell and Sha scrambled to maintain their business, the investigation was closing in.
By the time the boys began noticing the full extent of the disruptions, it was already too late. Their system, which had seemed impervious, was now riddled with vulnerabilities they couldn’t patch. The warning signs were clear, but the boys were too entrenched in their success to fully grasp the scale of what was coming.
For Darnell, the sense of unease was constant; for Sha, the setbacks were merely growing pains. In early 2022, the FBI, in collaboration with the security team of the affected platform, finally closed in on Darnell and Sha. Agents had pieced together a clear trail of evidence linking the two boys to the fraudulent creation and resale of accounts. One February morning, both of their homes were raided simultaneously. Darnell’s encrypted laptop, Sha’s marketing scripts, and meticulous transaction logs were seized, along with other digital tools that had fueled their enterprise.
The sheer scale of the operation stunned investigators—over $2 million had been generated in a year by two teenagers. The arrests sent shockwaves through their families. Darnell’s mother, who had worked tirelessly as a nurse to provide for him, was devastated. She couldn’t reconcile the image of her studious, quiet son with the mastermind of such a sophisticated scheme. Sha’s parents, less involved in his daily life, expressed confusion and frustration. Both families were blindsided, forced to grapple with the legal and financial fallout.
Prosecutors presented evidence that highlighted the technical expertise and precision of the operation—the automated scripts, the anonymous payment systems, and the professional branding. Yet the defense argued that the boys’ age and inexperience had played a role in their actions. Their lawyer emphasized that they hadn’t hacked into accounts directly or stolen data themselves, but had instead exploited existing loopholes. It was also noted that Darnell and Sha had cooperated fully with investigators after their arrests, providing key details.
The court faced a difficult decision. On one hand, the scale of the scam and its impact warranted serious consequences. On the other, the boys had no prior criminal history and had demonstrated remorse. Ultimately, the judge opted for leniency, taking into account their cooperation, age, and potential for rehabilitation. Instead of juvenile detention, they were sentenced to 1,500 hours of community service each, a five-year probationary period, and mandatory participation in a financial literacy program. Restitution payments were also imposed, requiring the boys to work toward repaying the stolen funds over time.
The story became public news, serving as both a cautionary tale and a commentary on the pressures faced by youth in disadvantaged communities—how ingenuity and ambition, when unchecked by guidance, could spiral into illegal activities. In the months that followed, the boys began their community service, working in programs aimed at educating other young people about the risks and consequences of cybercrime.
For Darnell and Sha, the consequences were a reminder of how quickly their dreams of success had turned into a hard lesson about accountability and the limits of ambition. Their story, born of hope and ingenuity, ended not in triumph, but in a lesson that would linger far beyond the headlines—a lesson about the power of guidance, the importance of integrity, and the unpredictable consequences of chasing shortcuts to success.
News
Gayle King speaks out on Nancy Guthrie’s disappearance: ‘Somebody knows something’
Gayle King is once again speaking out on the disappearance of Savannah Guthrie’s mom, Nancy Guthrie. “Somebody knows something,” the…
The identity of the imposter who sent the ransom letter claiming to be Nancy Guthrie has been revealed, and his testimony is shocking
A California man accused of sending phony ransom texts to Savannah Guthrie’s family about her missing mother has been arrested…
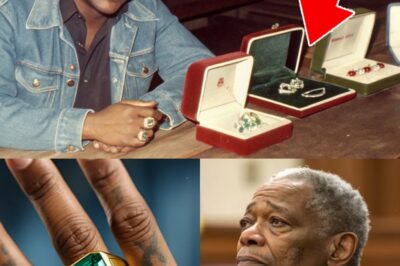
$1,6M Vanished in a 1982 Museum Theft — 35 Years Later, A Ring Surfaced in a Rap Video
In 1982, a priceless art deco jewelry collection vanished overnight from a traveling exhibition in Miami. No alarms sounded, no…
$850K Blackmailed From Factory Owner in 1990 — 3 Years Later, Press Recording Revealed the Truth
In 1990, a metal factory owner in Chicago received a demand for $850,000 in cash, accompanied by threats to expose…
She Won $265K at the Slots in Vegas in 1994 — Seven Days Later, Her Husband Was K!lled
A week after a Detroit warehouse supervisor hit a life-changing jackpot in Las Vegas, her husband was found dead on…
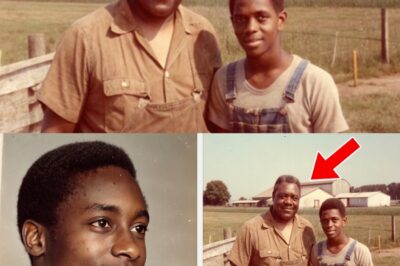
Young Man Vanished in 1980 — 10 Years Later, a Flea Market Find Reopened His Case
He hitchhiked across the South with nothing but a backpack, a plan, and a promise to call his sister when…
End of content
No more pages to load